-
Notifications
You must be signed in to change notification settings - Fork 81
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Integration tests executed on a real deployment as part of the CICD - Redshift Connections #1628
Conversation
b21c8da to
57d4e2b
Compare
57d4e2b to
d658890
Compare
2a3108e to
eaa2d53
Compare
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
Still need to test - setting that up now
But left some comments on code review in the meantime
tests_new/integration_tests/modules/redshift_datasets/test_redshift_connection.py
Outdated
Show resolved
Hide resolved
tests_new/integration_tests/modules/redshift_datasets/test_redshift_connection.py
Outdated
Show resolved
Hide resolved
tests_new/integration_tests/modules/redshift_datasets/test_redshift_connection.py
Outdated
Show resolved
Hide resolved
tests_new/integration_tests/modules/redshift_datasets/test_redshift_connection.py
Outdated
Show resolved
Hide resolved
tests_new/integration_tests/modules/redshift_datasets/test_redshift_connection.py
Show resolved
Hide resolved
|
got all 30 tests passed after ensuring |
…1638) ### Feature or Bugfix - Bugfix - Refactoring ### Detail - Rename MANAGE_REDSHIFT_CONNECTION_PERMISSIONS as EDIT_REDSHIFT_CONNECTION_PERMISSIONS to avoid confusion with Tenant permissions that are always defined as MANAGE.... - Limit the groups that can be granted connection permissions to those groups in the same Environment - Adjust unit tests accordingly ### Relates - #1628 ### Security Please answer the questions below briefly where applicable, or write `N/A`. Based on [OWASP 10](https://owasp.org/Top10/en/). - Does this PR introduce or modify any input fields or queries - this includes fetching data from storage outside the application (e.g. a database, an S3 bucket)? - Is the input sanitized? - What precautions are you taking before deserializing the data you consume? - Is injection prevented by parametrizing queries? - Have you ensured no `eval` or similar functions are used? - Does this PR introduce any functionality or component that requires authorization? - How have you ensured it respects the existing AuthN/AuthZ mechanisms? - Are you logging failed auth attempts? - Are you using or adding any cryptographic features? - Do you use a standard proven implementations? - Are the used keys controlled by the customer? Where are they stored? - Are you introducing any new policies/roles/users? - Have you used the least-privilege principle? How? By submitting this pull request, I confirm that my contribution is made under the terms of the Apache 2.0 license.
|
Hi @noah-paige I added a new test and tested all of them again locally: Because I am playing a bit with the invitation to environments/organizations I will run the tests on a real AWS CICD pipeline |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
tested on my end as well and looks good
… Redshift Datasets (#1636)⚠️ MERGE AFTER #1628 ### Feature or Bugfix - Feature: Testing ### Detail Add integration tests for Redshift datasets It also includes the global conftest fixtures that will be used for redshift dataset sharing At the moment it assumes Redshift infrastructure is already provided; we might want to implement the deployment of this pre-required infra, but that can be done on a separate PR. ## Testing Tested locally: 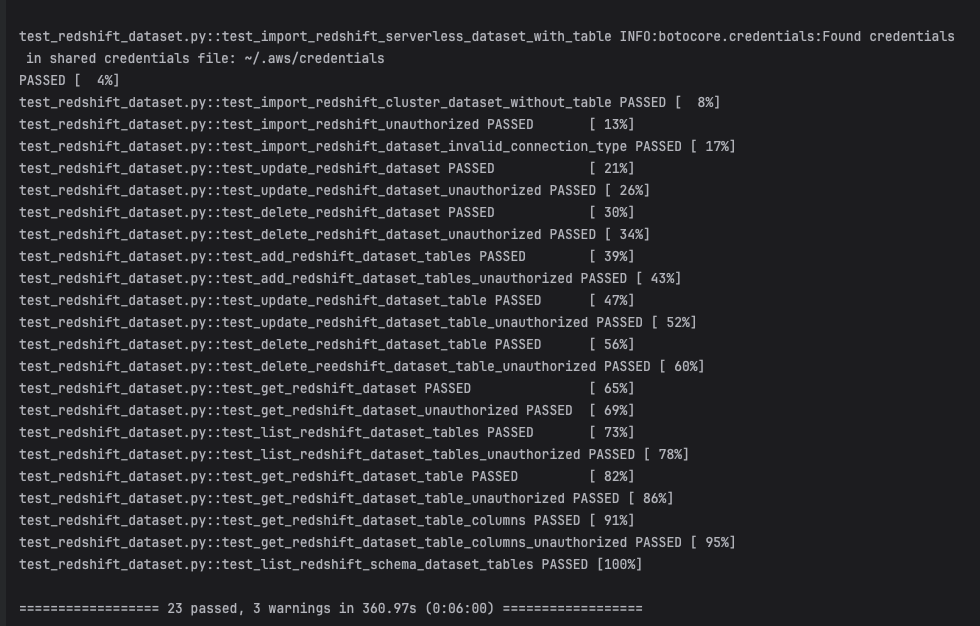 ### Relates - #1619 - #1220 ### Security Please answer the questions below briefly where applicable, or write `N/A`. Based on [OWASP 10](https://owasp.org/Top10/en/). - Does this PR introduce or modify any input fields or queries - this includes fetching data from storage outside the application (e.g. a database, an S3 bucket)? - Is the input sanitized? - What precautions are you taking before deserializing the data you consume? - Is injection prevented by parametrizing queries? - Have you ensured no `eval` or similar functions are used? - Does this PR introduce any functionality or component that requires authorization? - How have you ensured it respects the existing AuthN/AuthZ mechanisms? - Are you logging failed auth attempts? - Are you using or adding any cryptographic features? - Do you use a standard proven implementations? - Are the used keys controlled by the customer? Where are they stored? - Are you introducing any new policies/roles/users? - Have you used the least-privilege principle? How? By submitting this pull request, I confirm that my contribution is made under the terms of the Apache 2.0 license.

Feature or Bugfix
Detail
Add integration tests for Redshift connections
It also includes the global conftest fixtures that will be used for redshift-datasets and redshift dataset sharing
At the moment it assumes Redshift infrastructure is already provided; we might want to implement the deployment of this pre-required infra, but that can be done on a separate PR.
+++ Additional fixes found during testing and fixed in this PR
Testing
Relates
Security
Please answer the questions below briefly where applicable, or write
N/A. Based onOWASP 10.
fetching data from storage outside the application (e.g. a database, an S3 bucket)?
evalor similar functions are used?By submitting this pull request, I confirm that my contribution is made under the terms of the Apache 2.0 license.