credit to
https://twitter.com/R00tkitSMM ([email protected]) telegram username : https://telegram.me/firozi
some day ago i found vulnerability in win10pcap Driver that can lead to Privilege escalation i report vulnerability and now bug is fixed :
so i decide to publish sample exploit
Win10Pcap is a new WinPcap-based Ethernet packet capture library. Unlike original WinPcap, Win10Pcap is compatible with NDIS 6.x driver model to work stably with Windows 10. Win10Pcap also supports capturing IEEE802.1Q VLAN tags.
so if you install wireshark on window 10 you need this shit :)
Win10Pcap kernel-mode driver did not check the virtual addresses which are passed from the user-mode , IOCTL Using Neither Buffered Nor Direct I/O without ProbeForWrite to validating passed address
you need find accurate Device name in runtime to send IOCTL , hardcoded device name dont lead to vulnerable code
IOCTL handller write a string in passed address , string is something like "Global\WTCAP_EVENT_3889023063_1"
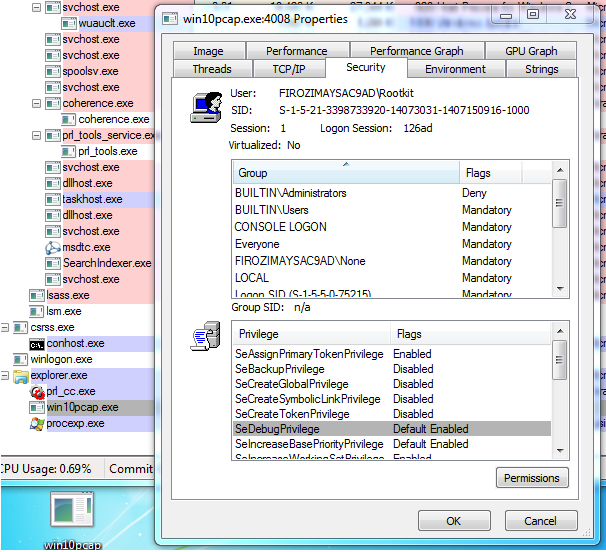
ther was many way to exploit this vulnerability i decide to set privilege in process TOKEN with overwriting _SEP_TOKEN_PRIVILEGES
overwriting token at address 0x034 with string "Global\WTCAP_EVENT" can set SeDebugPrivilege without corrupting sensitive Filds
81687cf8 cc int 3
2: kd> dt nt!_TOken
+0x000 TokenSource : _TOKEN_SOURCE
+0x010 TokenId : _LUID
+0x018 AuthenticationId : _LUID
+0x020 ParentTokenId : _LUID
+0x028 ExpirationTime : _LARGE_INTEGER
+0x030 TokenLock : Ptr32 _ERESOURCE
+0x034 ModifiedId : _LUID
+0x040 Privileges : _SEP_TOKEN_PRIVILEGES
+0x058 AuditPolicy : _SEP_AUDIT_POLICY